[fusion_text]Security is the ultimate goal of Microsoft Azure as customers want a highly protected environment for work. SSL 3.0 was a major vulnerability observed in Azure machines and websites. It was not limited to one or two types of machines, but all websites and Windows Virtual machines got vulnerable. To ensure the safety of the users, Microsoft completely disabled SSL 3.0 in Azure Websites by default to protect customers from the vulnerability.
Disable SSL 3.0 in Azure Web Or Worker Roles:
Redeploying the application is the best way to make changes in Azure Platform as Service (PAAS). This method ensures that all instances have access to configuration and it has the capacity to survive the service healing operations.
Step 1: Build the Startup Script
In the first step, you need to create a DisableSslv.cdm file and place the file in each directory. No need to perform this step if you are using updated version as Azure has updated servers with optionally set SSL cipher.
Now, create another file with name DisableSslv3.ps1 and place it in Startup directory of the role’s definition.
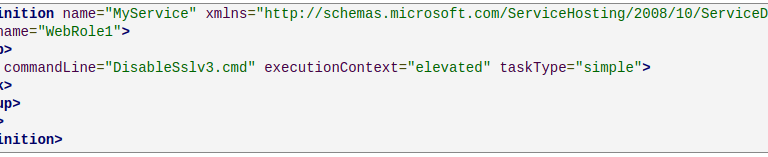
Step2: Add Startup Task in Role’s Definition
Disable SSL 3.0 in Azure Virtual Machines
The PowerShell script provided for Azure Roles works for disabling SSL 3.0 on Windows Virtual Machines as well. The script can be manually run over Remote Desktop Protocol or any other infrastructure configuration management system.